

The E4 is a thermal infra-red camera made by
FLIR - see e.g.
E4, E5, E6, and E8 cameras.
It ships with a USB cable which serves both as charger and data cable - the
camera appears as a USB flash drive in the same manner as many regular
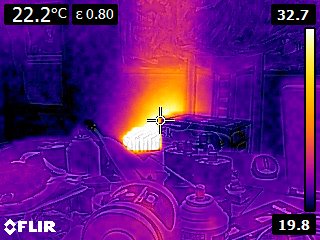
cameras. In the mode I use, taking a picture gives a pair of JPEG
images, a normal visible-light photograph of 640x480 pixels, and a false-colour
infrared photograph of 320x240 pixels.
The documented infrared resolution of the camera is 80x60 pixels, so the
saved image is interpolated out to 320x240.
Many contributors to the eevblog.com forums have investigated the workings of these cameras. In particular, the threads flir-e4-thermal-imaging-camera-teardown, flir-e4-the-useful-information-thread/ and flir-e4-teardown-qa-and-newbie-questions have a wealth of detail. Most of this is targetted at Windows users; the camera itself uses Windows CE, and there is a Windows toolkit from FLIR at FLIR Tools for PC and Mac.
A "hidden menu" is described in the forum threads; this is accessible
under Settings/Device Settings/Camera Information by pressing and holding
the right cursor for some ten seconds. A new menu appears with
USB mode, Export information and Version information.
USB mode offers a choice of MSD (mass storage device) - the normal setting,
UVC (USB video class),
RNDIS (Remote Network Driver Interface Specification), or a combination.
In UVC mode, the camera operates as a webcam and appears as /dev/videoN using the
V4L2 interface. Software such as Cheese
can be used to capture images and video. Video capture did not work for me,
though I was able to use mencoder (from
mplayer), viz.
mencoder -tv device=/dev/video1 -ovc copy -o out.avi tv://1
In RNDIS mode, the camera appears as a virtual ethernet device on e.g. eth6, at address 192.168.250.2. Although DHCP over RNDIS works on e.g. the BeagleBone Black, it would not work for me on my E4. Instead, I configured NetworkManager for address 192.168.250.1, netmask 255.255.255.0, gw 0.0.0.0, method manual, and could then access the E4 at 192.168.250.2 with ftp and http. Ftp gives access to the device memory either as anonymous or with username/password flir/3vlig. A lot of information such as the MAC address was logged to syslog when the camera was connected, e.g. /var/log/messages.
A method for modifying the E4 configuration file is described in forum messages such as teardown/msg403480. The exact method depends on the firmware revision. Some tools are provided, with sourcecode, e.g. at tools1.zip.
These compile fairly easily in Linux. However, though CRC03 appears to work properly, ftool I found did not create the correct 16-byte MD5 hash when run in encryption mode. The Windows executable ftool.exe runs properly in Wine.
So, the procedure is roughly as follows, for firmware revision 1.21/1.22:
- $ wget ftp://192.168.250.2/FlashFS/system/appcore.d/config.d/conf.cfc
- $ cp conf.cfc conf.cfc.original
- $ ./ftool -d conf.cfc conf.txt (note the keys)
- edit conf.txt, removing the existing "# CRC03" line
- $ ./crc03 conf.txt >> conf.txt (remove "Add the following.." from the source or from the resulting output)
- $ wine ftool.exe -e conf.txt conf.cfc key1 key2
- Upload the new conf.cfc with ftp, in binary mode (important!)
- power off the E4 and do a cold start (remove the battery for several seconds)