TPod sonar logging

The Sonarphone T-pod is a battery-operated echo sounder (fish finder) that communicates with a phone or tablet over WiFi. The phone app (Android or iPhone) displays depth on the phone screen, as on a traditional standalone sounder screen:
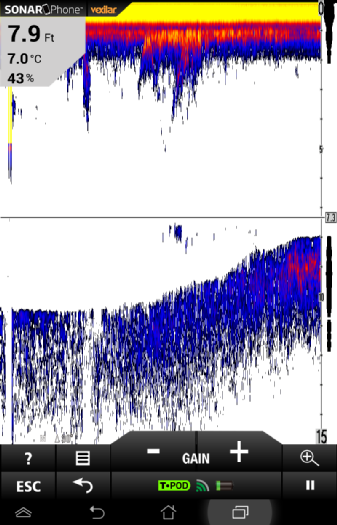
However, the app does not log data. This can be a serious inconvenience, for instance if creating a chart from GPS data.
Fortunately, raw sonar return data can be derived from the network data stream.
The T-Pod works by creating a WiFi access point, which the display device connects to. The
T-Pod assigns the private address 192.168.1.1 to itself and 192.168.1.100 to the display,
and then sends depth data encoded as UDP packets on port 5000. The data record
consists of some 40 bytes of metadata such as water temperature and operating
range, followed by some 300 bytes of sonar return intensity data, one depth interval
per byte.
It is possible to record this data with the Unix program tcpdump, available for Android. (It may be necessary to use a jailbroken device with root access). tcpdump runs readily via the Android debugger adb, but not so easily from the display. Without root privilege, it runs, but cannnot capture data. I was able to login via an SSH client to root@localhost - an SSH server running on my tablet. Since that was awkward to use, I made a copy of tcpdump with the suid bit set (as for the standard "ping" program) so I could run it from an unprivileged command-line app, e.g.
shell@android:/ $ ls -l /system/bin/tcpdump2 -rwxr-sr-x root net_raw 1287649 2016-02-20 23:21 tcpdump2A utility script tpcap runs this, creating a capture file on the SD card with a time-based filename.
The resulting libpcap format data can be decoded using a variety of tools such as Wireshark. Te following scripts use the perl Net::Pcap module to read the pcap data file directly.
- tpodcap2png.pl - create PNG image from Tpod pcap data
- tpodcap2dat.pl - convert Tpod data metadata to gnuplot data file
- tpodcap2dat3d.pl - convert Tpod pcap data to gnuplot 3D datafile
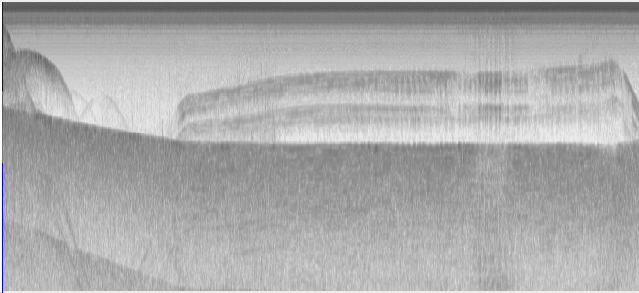
PNG image of raw return data, from tpodcap2png.pl
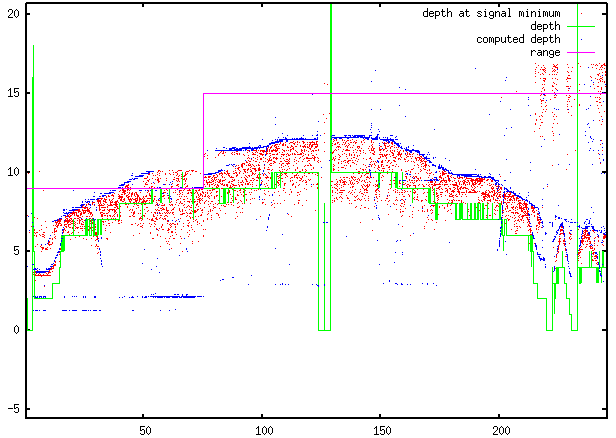
Plot of metadata and computed depth, from tpodcap2dat.pl
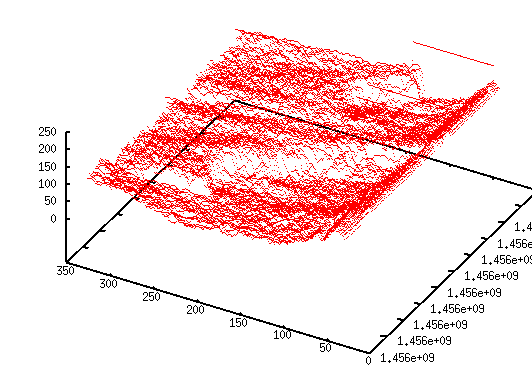
3D plot, return intensity against time and depth, from tpodcap2dat3d.pl